
Roaming Experience for Large-Scale Events
Mobileum’s GlobalRoamer® solution proactively tests and monitors roaming QoS during major events like the Olympics and World Cup, ensuring reliable connectivity and customer satisfaction.
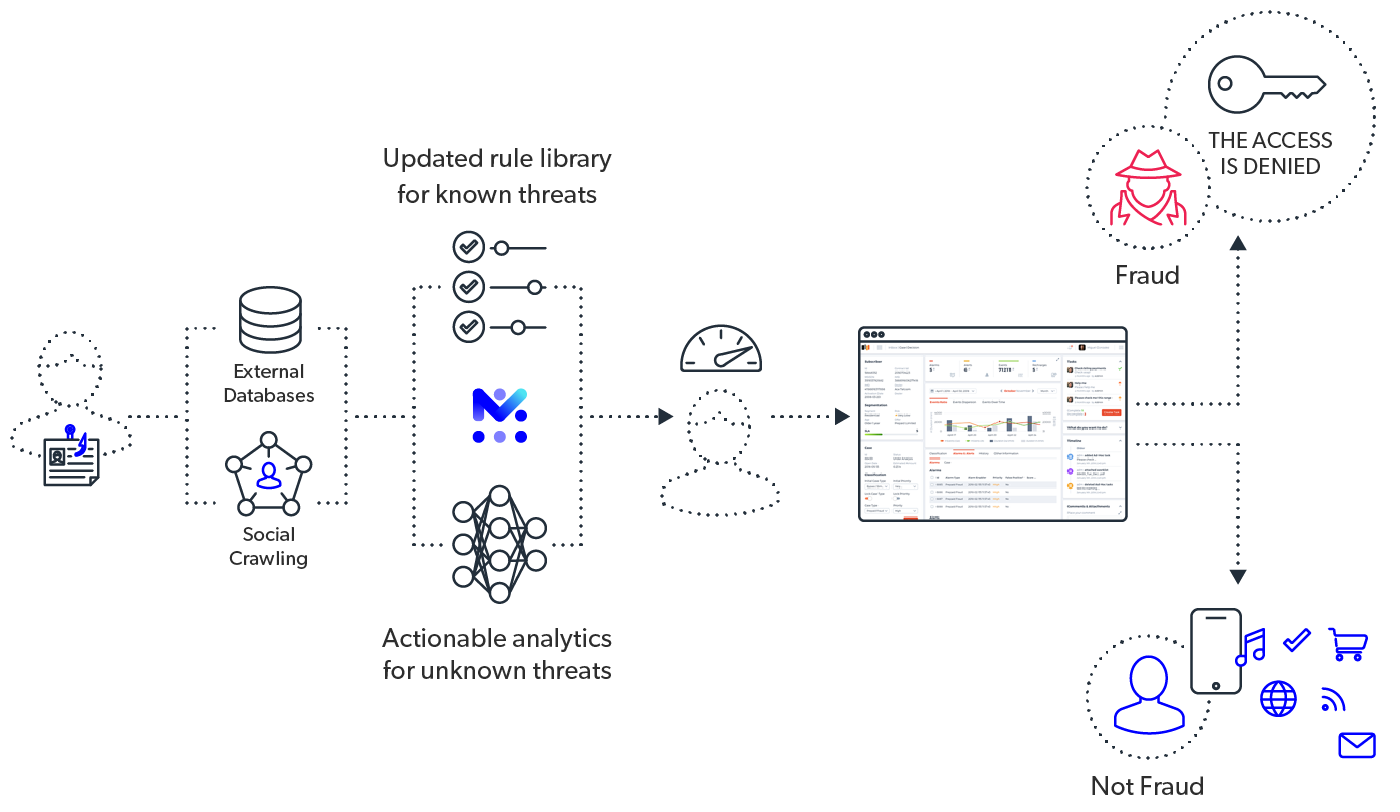
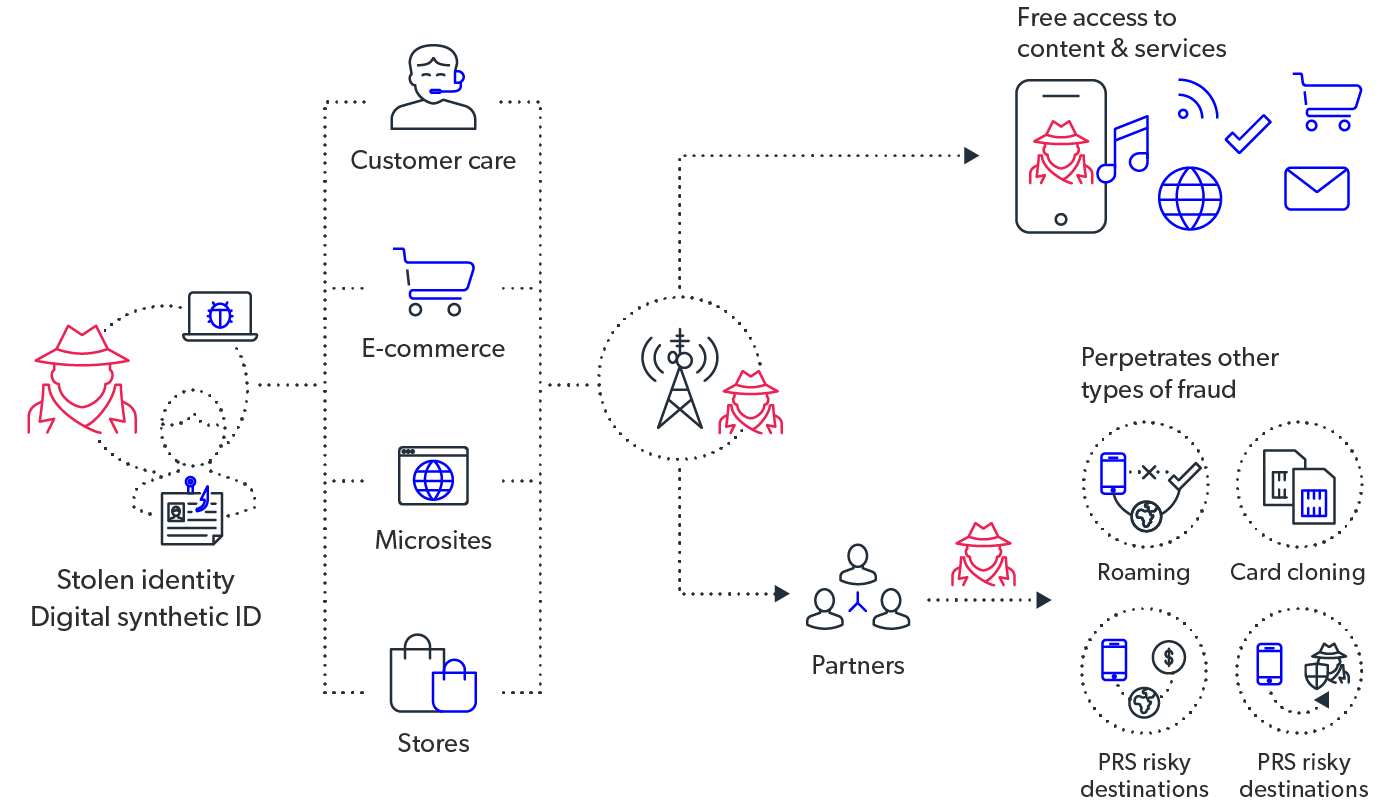
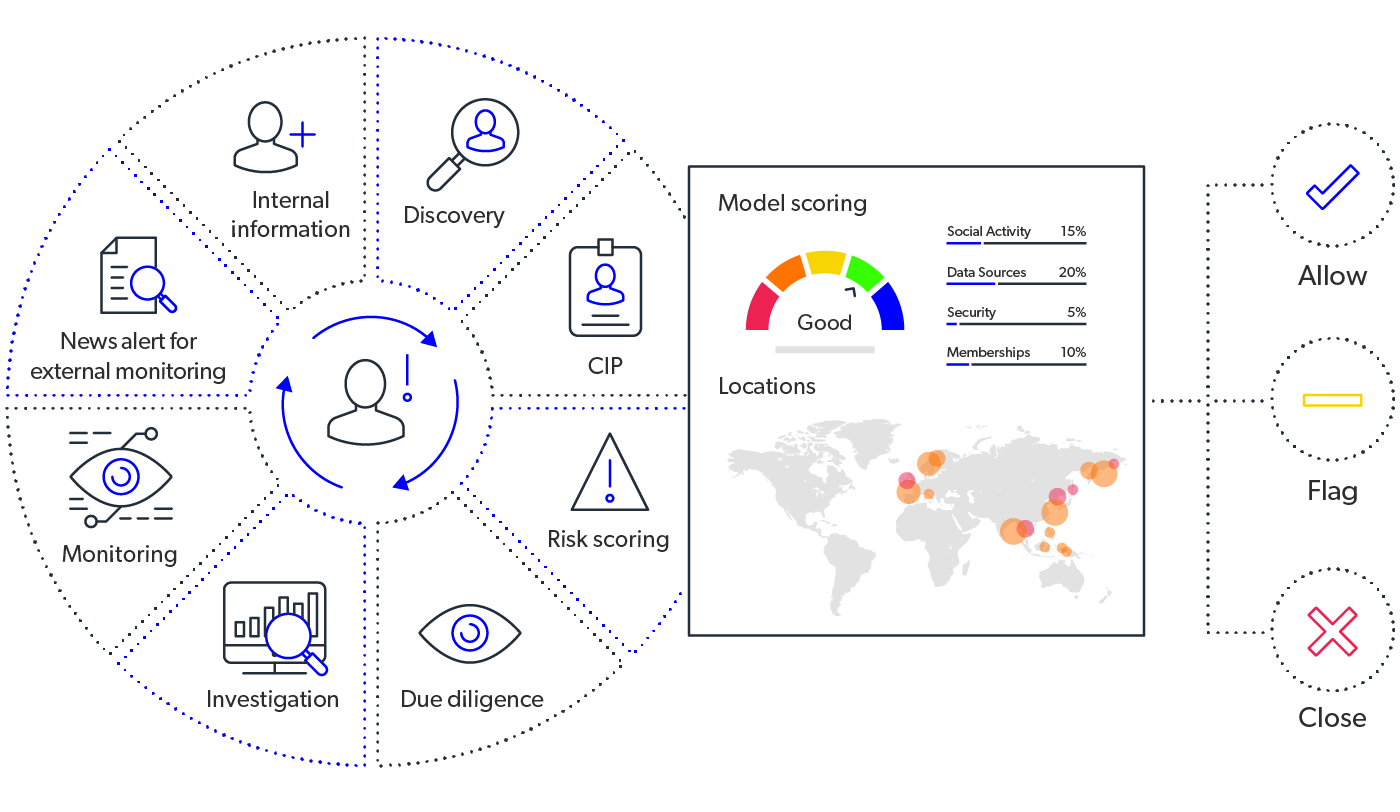
Telecom operators face increasing threats from fake accounts, identity theft, and promotional abuse. Mobileum's Subscription Fraud solution leverages advanced AI to proactively detect and stop fraudulent activities before they impact your business.


Mobileum’s Subscription Fraud solution leverages advanced analytics and real-time intelligence to protect telecom operators from subscription-based fraud, safeguarding subscriber acquisition processes and revenue streams.
Fraudulent subscriptions cost operators millions in revenue annually. Mobileum ensures secure subscriber onboarding, reduces fraud-related losses, and enhances subscriber trust through intelligent, automated fraud detection.
Seamless Subscription Fraud Protection with RAID
Ensures risk detection and mitigation through the RAID Risk Library
Correlates risk monitoring intersections and compliance across different risk threats
Regular updates to the risk catalog align with evolving threats and regulations
Enhances fraud detection, compliance, and risk mitigation with AI-driven automation



Reduce subscription fraud revenue loss by up to 40%.
Improve subscriber satisfaction by proactively preventing identity theft and misuse.
Automate detection to lower fraud management costs by 30%.
Trusted by 1,000+ operators worldwide
Proven expertise in telecom risk management and revenue assurance
AI-powered automation for risk and revenue assurance
Seamless integration with existing telecom infrastructure

Mobileum’s GlobalRoamer® solution proactively tests and monitors roaming QoS during major events like the Olympics and World Cup, ensuring reliable connectivity and customer satisfaction.