
Competitive Benchmarking
Mobileum’s Competitive Intelligence empowers telecom operators with real-time benchmarking to optimize service performance, investments, and positioning.
Explore Mobileum’s Deep Packet Inspection (DPI) for Cyber Security — detect threats in real time, decode traffic, and ensure compliance across telecom networks.


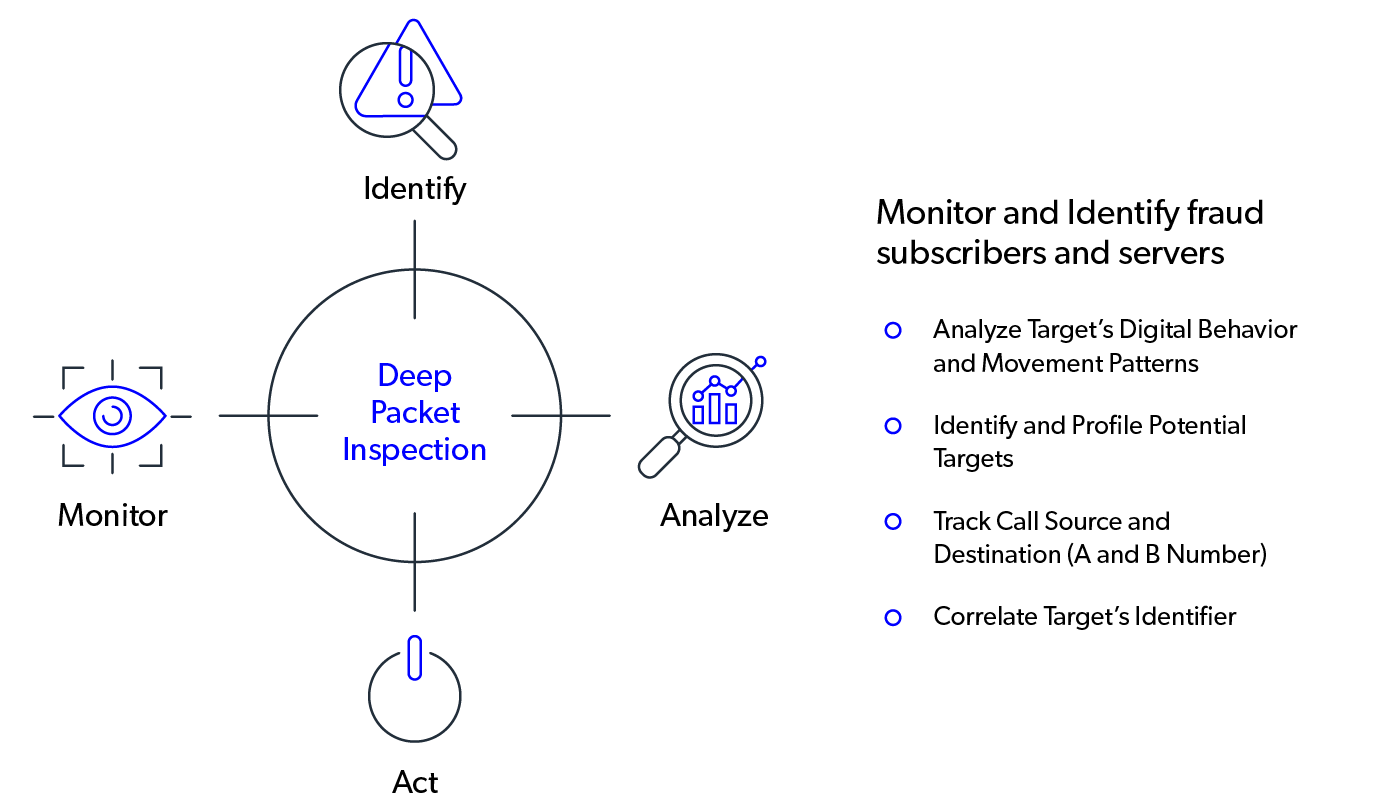
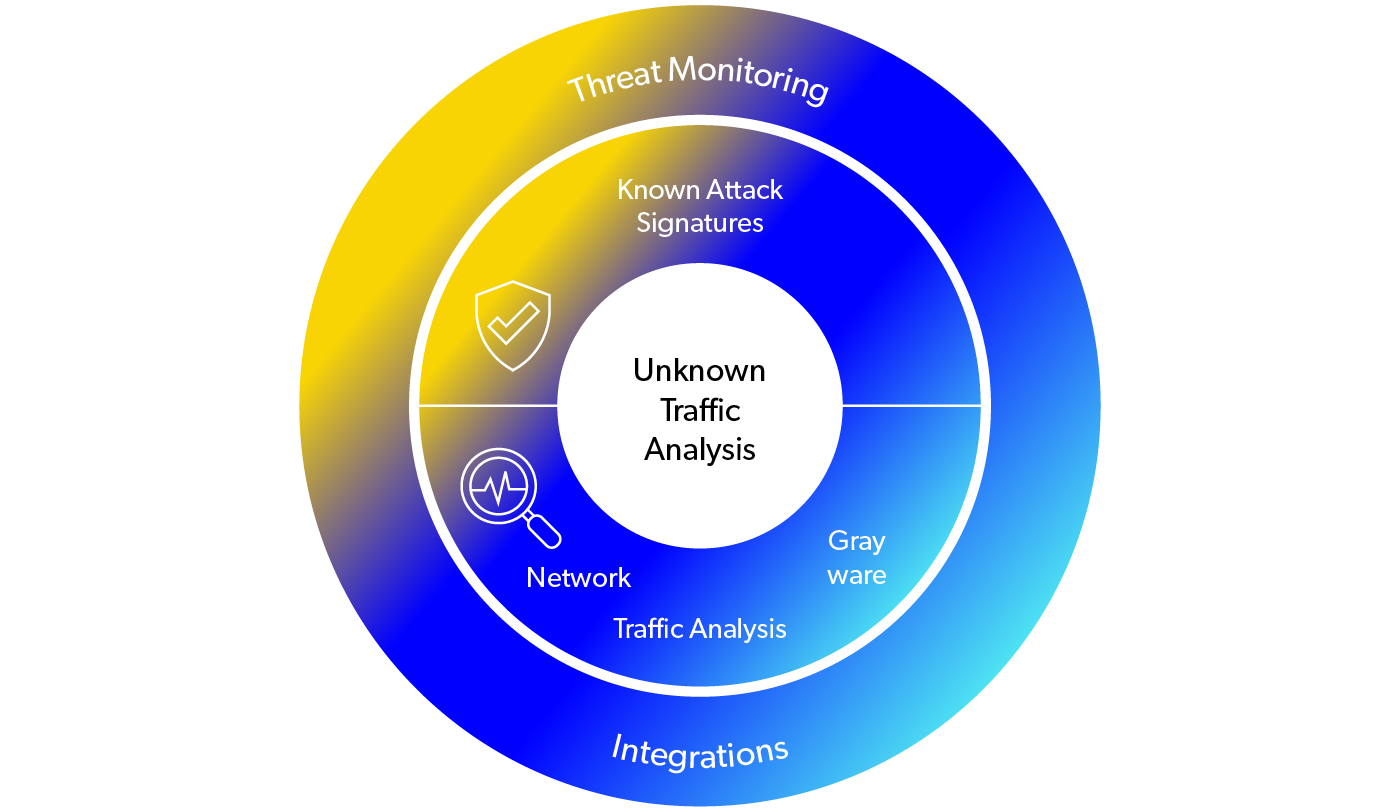
Mobileum’s Deep Packet Inspection (DPI) solution uses advanced analytics and AI to decode encrypted and non-standard traffic across telecom networks. It extracts rich metadata and correlates behaviors across protocols to deliver deep visibility into subscriber activity.
Traditional monitoring tools can’t keep pace with encrypted traffic and evasive apps. Mobileum’s DPI delivers real-time threat detection, identifies malicious patterns, and ensures compliance with IP data regulations. It fills the visibility gap caused by encryption and tunneling, allowing CSPs to act with confidence and speed.
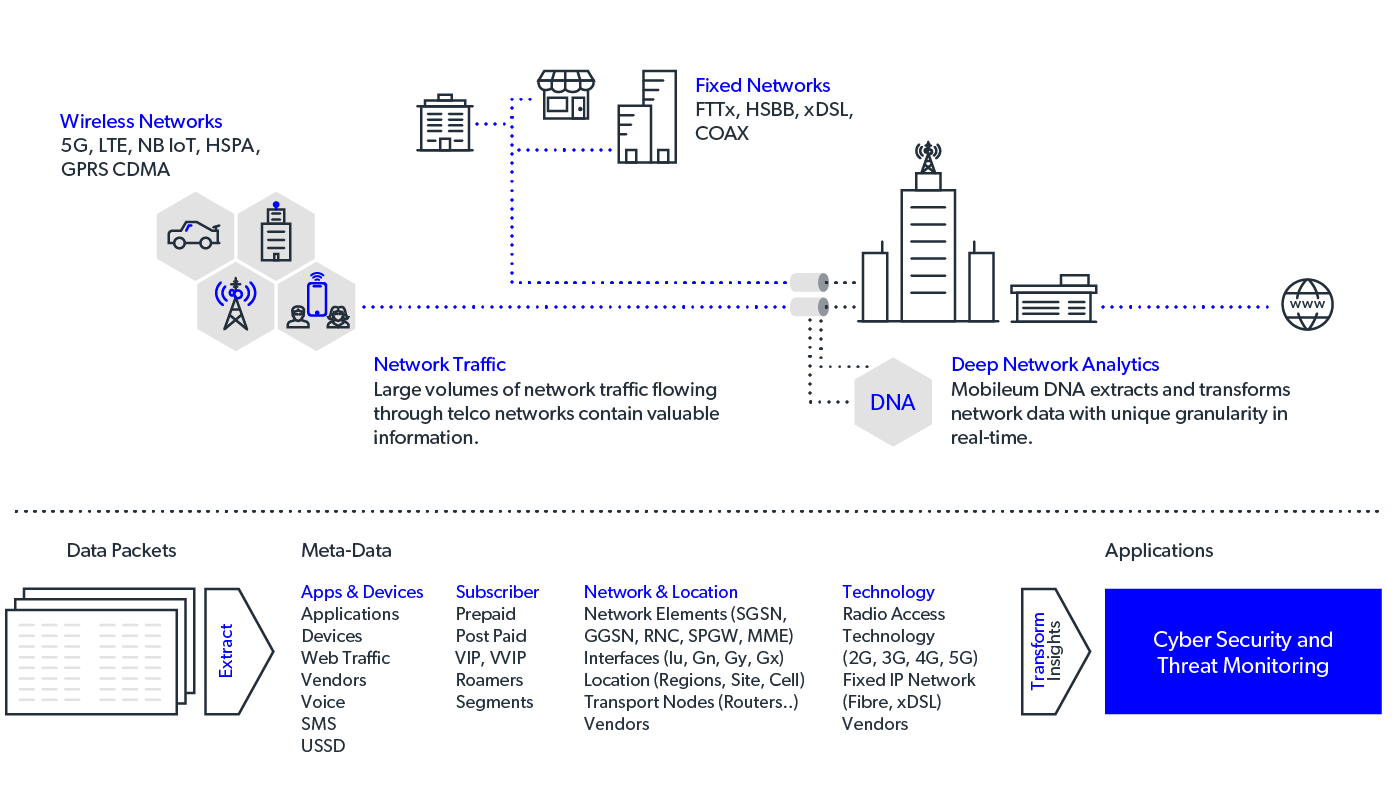



Encrypted traffic insights for 5G & fixed networks.
Faster queries help prevent or react to incidents.
Reduces storage and processing up to 80%.
Trusted by 1,000+ operators across 190+ countries
AI-powered defense for signaling, voice, SMS, and data
Block attacks as they happen — with zero manual lag
Cross-protocol protection for 2G to 5G, VoLTE, and IoT

Mobileum’s Competitive Intelligence empowers telecom operators with real-time benchmarking to optimize service performance, investments, and positioning.